Two-factor authentication and single sign – on 5 free 2FA systems for retrofitting
Two-factor authentication and single sign-on systems are state-of-the-art among the big players on the net. With free software, however, you can also secure your own apps and infrastructures, if desired without any third parties.
Company about the topic
 The 2-factor authentication known from the web can also be integrated into own team projects with prefabricated solutions.
The 2-factor authentication known from the web can also be integrated into own team projects with prefabricated solutions.
(© chinnarach – stock.adobe.com)
The development of your own applications is already time-consuming enough, who wants to take care of the topic of security unduly? Especially when it comes to company – internal apps and no own IT let alone IT security department is available, then the built-in password query of the distributed access database is used again.
But fun aside. Whether it’s internal processes, SaaS offerings or stationary end-user apps, proper authentication is essential as soon as confidential or personal data are generated. And today this also includes a solution for two-factor authentication (2FA), as you know it all too well from logging in to your Google account or paying via Paypal.
By the way, the whole thing also has a huge advantage from the user’s point of view: By logging in with a username/password and a temporary one – time password, a hardware token or the like – which has long been customary for most people-annoying complicated regulations for passwords can be omitted.
Fortunately, there is a huge selection of free projects around the topic 2FA, which often also cover Single Sign On (SSO). The effort depends heavily on the applications to be protected. By the way, you don’t have to worry too much about the client side, here there are established tokens such as YubiKey USB sticks or the omnipresent Google Authenticator for TOTPs, which is supported almost everywhere.
On the wish list of authentication methods are often the standards SAML, OpenID Connect and OAuth2, which are usually found at least in the larger solutions. Here we would like to briefly present five tools that are worth a closer look: two full-fledged, commercially backed SSO complete systems, two web-based 2FA solutions and a pure PHP implementation of the 2FA principle.
Google2FA
Google2FA is a PHP implementation of Google’s two-factor authentication module and, despite its name, is not affiliated with Google. It is by far the smallest project in this collection and is really only dedicated to its core task.
Google2FA generates the shared secret, makes it available to clients such as Google Authenticator via QR codes and verifies their returned one-time passwords of the TOTP and HOTP forms. Actually, QR code generation is even taken over by external tools.
Google2FA exemplifies for other libraries that two-factor authentication is not too complicated in its basic form. However, it also shows how 2FA can be integrated into your own apps, while all of the following systems aim to serve as intermediary platforms between existing applications and users.
Authelia
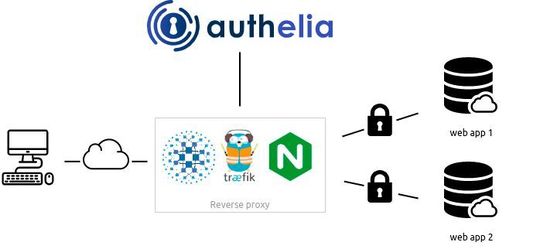 Authelia: Switching via reverse proxy.
Authelia: Switching via reverse proxy.
(Image: Authelia)
The beginning of the complete systems is made with Authelia a still quite young, small newcomer. Since 2017, the project has been regularly maintained by only two or three core developers. Authelia basically works like the big ones in the league, but many functions are still missing, which should be required in large infrastructures, from any graphical administration to data exchange via OpenID Connect or SAML-OpenID Connect is on the roadmap.
However, Authelia works out-of-the-box very well for securing web applications and is above all easy to understand: it switches between reverse proxies such as Traefik or Nginx and the domains to be protected and offers users a simple login interface for username/password and second factor, here TOTP or YubiKey USB sticks.
Keycloak
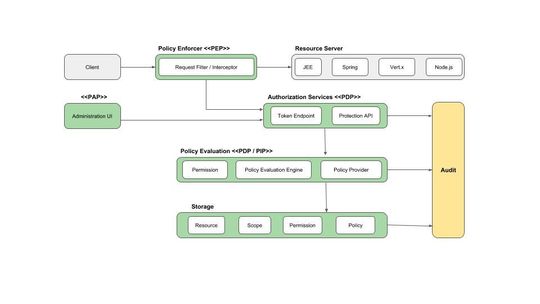 The Keycloak-Architecture.
The Keycloak-Architecture.
(Picture: Keycloak)
Keycloak is a full-fledged identity and access management tool under the auspices of Red Hat and has been around since 2014. Keycloak focuses on single sign-on functionality.
The platform works with Kerberos, enables authentication via social platforms and any OIDC and SAML provider, connects to LDAP and Active Directory, and provides role-based rights allocation. Clients are protected via so-called adapters, basically libraries. Derlei offers the Java-based Keycloak among others for Tomcat, WildFly, Node.js, oidc (Python), AppAuth (Android/iOS) and OWIN (C#).
This makes Keycloak a framework for almost any in-house development. 2FA is also supported, but by default only TOTP via the Google Authenticator or alternatively FreeOTP. However, other second factors such as U2F or SMS push messages can be integrated via third-party projects.
Gluu
 Registered devices in the Gluu Server.
Registered devices in the Gluu Server.
(Image: Gluu, Inc.)
The Gluu Server is similar to Keycloak in many Parts: Mature Java product with a graphical Management interface, SSO for any Web and Mobile applications, Social Login, SAML, and OpenID support, fine-grained permissions, user management via LDAP and AD, Installation with Docker/Kubernetes, access via web interface and API, and so on.
Gluu Server already exists since 2010, is managed by Gluu, Inc. in Texas, Keycloak manages and can provide very good documentation-which is quite necessary due to the complexity. On the 2FA side, however, the two systems differ significantly: Gluu Server supports FIDO 2, TOTP/HOTP and Duo Security, but with Super Gluu also brings its own second factor in the form of an app for Android and iOS.
privacyIDEA
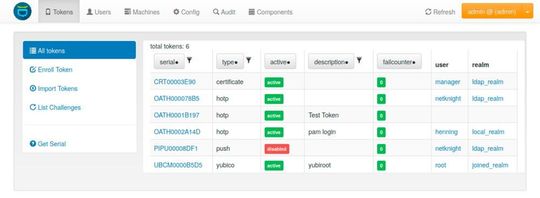 Token management in privacyIDEA.
Token management in privacyIDEA.
(Picture: privacyIDEA)
privacyIDEA is a Kassel-based project that clearly has its roots in the 2FA sector and is not a monolithic SSO solution. This can already be seen in the fact that privacyIDEA offers connections for Keycloak, Gluu and other systems.
privacyIDEA im is essentially developed by the IT security company NetKnights, which also offers paid versions and support. At this point it is important to know that privacyIDEA is offered under the AGPL, which adapts the copyleft concept of the GPL for SaaS: if you use privacyIDEA in the open source version, every user has the right to view the source code already with the use.
privacyIDEA can be used to extend existing logins and connections with a second factor, such as SSH connections, VPNs or even Windows logins-with the corresponding extensions. Apps such as Owncloud can also be secured directly via the plugin, but here only in conjunction with service contracts.
Originally privacyIDEA only supported OTPs, now challenge response procedures, U2F, SSH keys and even x509 certificates can also serve as a second factor. As sources for user accounts, privacyIDEA can access LDAP, Microsoft AD, SQL databases, text files and systems that support the System for Cross-domain Identity Management (SCIM) specification, such as Gluu.
privacyIDEA can’t quite keep up with the big SSO solutions in terms of documentation and community, but it does have its appeal when such a solution is already running and does not provide sufficient 2FA protection and of course to extend conventional logins-privacyIDEA itself emphasizes VPN logins via RADIUS servers.
privacyIDEA is definitely interesting, unfortunately the combination of open source, community, service contracts, plugins and NetKnights is not always very clear. Testing is also difficult because a linked demo has been disabled and the alternative live system is outdated and largely undocumented.
Summary
The five open source 2FA applications presented are certainly among the most well – known projects and cover a wide range of scenarios-whether for the protection of existing infrastructures or integration into newly developed projects. If you want to take a look further, you might want to take a look at LinOTP, a fully-fledged authentication solution, also from Germany, managed by arxes-tolina.
(ID:47182742)












